 Last year we told about not so well know tool called MDK, as part of the “Cracking WEP key – Acces Point with pree-shared key (PSK” concept. Alot of time has passed by since then and now we have well workiong stable version even with GUI extension Charon. It was not much of a deal in Fall 2007, but the situation has changed. The autor has also decidedd to eneble the Destruction Mode in the menu. The extension is written in Java and is very stable. If you have not encountered the MDK tool before, it is a proof-of-concept tool from the authors of the PTW implementation in aircrack-ng (Darmstadt Lab).
Last year we told about not so well know tool called MDK, as part of the “Cracking WEP key – Acces Point with pree-shared key (PSK” concept. Alot of time has passed by since then and now we have well workiong stable version even with GUI extension Charon. It was not much of a deal in Fall 2007, but the situation has changed. The autor has also decidedd to eneble the Destruction Mode in the menu. The extension is written in Java and is very stable. If you have not encountered the MDK tool before, it is a proof-of-concept tool from the authors of the PTW implementation in aircrack-ng (Darmstadt Lab).
It tses 8 concepts of attacking wireless networks.

b – Beacon Flood Mode sends beacon frames and confuses the client by creating fake APs. This is able to make AP scanning applications and devices unusable
a – Authentication DoS mode sends auth frames to all APs in range. This results in freezinig or restarting devices
p – Basic probing a ESSID Bruteforce mode sends probe requests to APs and checks replys
d – Deauthentication / Disassociation Amok Mode. Disconnects AP’s all clients
m – Michael shutdown exploitation (TKIP). Permanetnly interrupts all communication in the wireless network
x – Penetration test for 802.1X
w – WIDS/WIPS Confusion.
f – MAC filter bruteforce mode (works only on APs that use proper open auth denial)
The GUI interface makes clicking tool out of MDK and allows the use of the already mentioned Destruction Mode. Just so you know what really happens, it’s scenario is described below:
Destruction mode
Destruction mode combines several attacks. This attack renders IDS Cisco useless. On system that dont colapse, it at least breaks the routing table. In the last version, the proccess is semi-automatic.
1. Beacon flood generates fake Access Points with the victim’s SSID
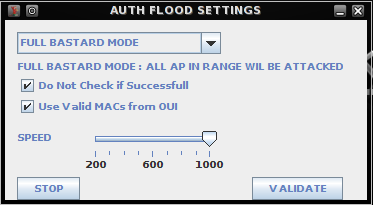
2. Auth-DoS floods victim’s AP with auth requests (ini inteligentnt mode)
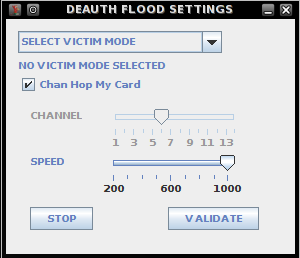
3. Amok mode dissasociates clients from the AP
4. WIDS confusion mód connects the clients via fake APs back to the ‘real’ AP
In result, noone is able to connect because Amok mode disconnects anyone who tries, clients detect thousands of AP with no clue on whichone is the realone. That will produce a nice beacon flood. The real AP will be too busy processing auth frames generated by Auth-DoS.
Interface description
Each mode opens a new interface. The main menu
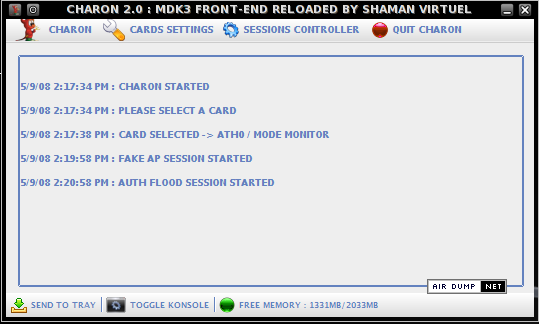
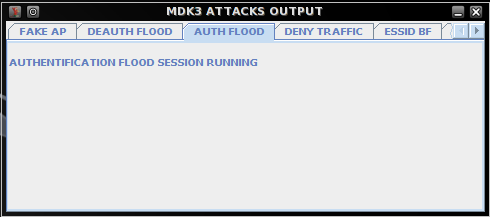
Charon Auth Flood mode
Charon Deauth Flood mode
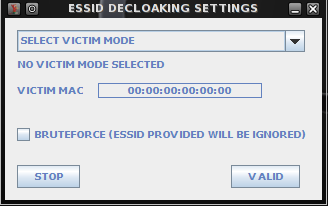
Charon Decloacking mode
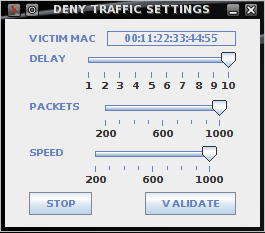
Charon Deny Trafic mode
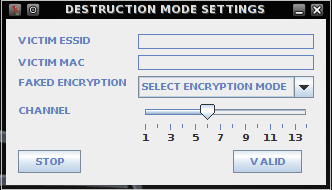
Charon Destruction mode
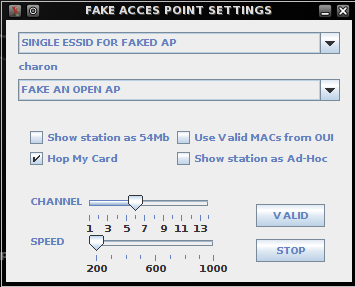
Charon Fake Access Point mode
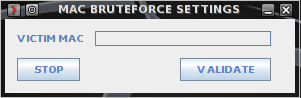
Charon MAC Brute Force mode
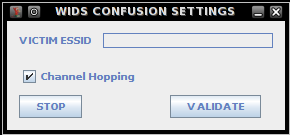
Charon WIDS mode
Every output has it’s own control panel.
Charon is available in lzm pack (ready out-of-the-box is only in Slackware), MDK wili run on any Linux based distribution. Charon with the latest versioin of MDK3 is available in the download section. Don’t forget the wlanconfig ath0 destroy / wlanconfig ath0 create wlandev wifi0 wlanmode monitor before pentesting (when full support of VAP cards such as Atheros will be done).
Corrently the supported chipsets are ipw3945 and rt73. Ps: The pack even includes airchucknorris-ng 3 , but well tell you about that next time.
Similar Posts:
- Aircrack 1.0 BETA .lzm BackTrack
- Capturing WPA-PSK handshake
- KoreK chopchop, Kismet, Gateway Ubuntu
- Sniffing networks and data analysis
- Intel Centrino Packet Injection WiFiSlax and ipw3945
- Evilgrade Toolkit helping with fake updates
- The Intuitive WiFi hacking GUI app for Ubuntu Linux
- Airgraph-ng graphing away Wi-Fi traffic
- Naked Edimax EW-7318USg – Photogallery
- The Browser Exploitation Framework (BeEF) pentesting tool for web browsers.


